Every day, you enter the Digital world called ‘Internet’ and probably meet or rub shoulders with a few cyber bad guys – Hacker or Scammer.
As a server administrator that manages all your incoming email traffic, we do our best to keep your Inbox away from those bad guys.
Our post-office refers to major Spam databases and custom Anti Spam mechanism to block these Hacker and Scammer, but potentially-malicious emails somehow manage to slip through our filters with a very standard and common content in business communication.
Here’s how to spot them:
A – Attachment Scam
Direct Damage: 😞
Future Damage: 😞😞😞😞😞
According to a published study, a gift-wrapped item influences the recipient to have a more favorable attitude towards opening the attachment.
When a recipient receives an email (from an unknown sender) that contains attachments such as PDF, Docs, etc, it can be an ill-intentioned email that baits the recipient to open it and download Malware without his or her awareness.
Here is an example of how the attachment scam will look like:

Suggestions:
- Make sure you trust the origin of the attachment, give the sender a call if possible.
- Scan with your updated Antivirus program if you really wish to open the attachment.
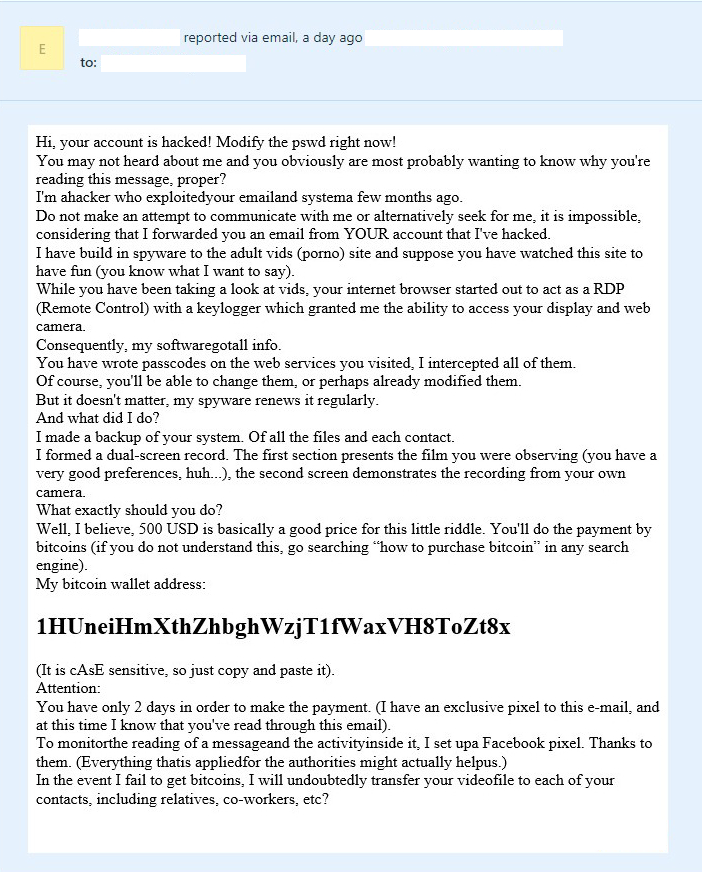
B – Bitcoin Blackmail Scam
Direct Damage: 😞😞😞😞😞
Future Damage: 😞
Bad guys or Scammers will use a different type of stories and techniques to write to you. They could even mask their email address so that you cannot trace back to their email address. Most of their email content contains blackmail element where they hold your important information and will ask for a ransom in order for you to get back your information.
Bitcoin is a cryptocurrency that does not record the sender and the receiver information, making the transaction completely anonymous. It is one of the reasons scammers choose this as a medium for their ransom. As a summary, strangers threaten you in exchange for bitcoins using a template warning.
Suggestions:
- Learn to differentiate the types of suspicious emails sent by unknown sender or companies. (Some can appear really genuine). If in doubt, don’t click or forward it to anyone in your contacts!
- Make sure you are browsing the internet in a safe network every time
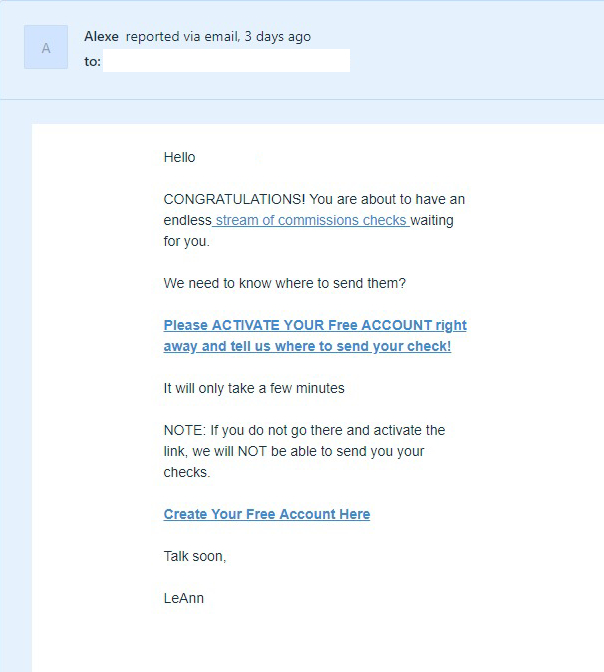
C – Checksum Scam
Direct Damage: 😞
Future Damage: 😞😞😞😞
Scammers attempt to send you an email that requests your confirmation on certain registration, login verification or system false alert such as mailbox full. These type of email are getting smarter, they will craft their content to look like the real company that sends you the email. It baits victims to click on a link to download certain malware or key in their details and plan for their second attack. Here is another one of the example:
Suggestions:
- If you did not register, ignore it.
- Check with your email service provider or vendor on the false alert.
D – Domain Scam
Direct Damage: 😞😞😞😞
Future Damage: 😞
When you register a new domain, your personal information is published to the WHOIS directory, which is available to anyone.
Scammers collect these details and try to scam the domain owner with content such as domain expiry date or SEO submission that requires you to make the additional payment.
Suggestions:
- Get protected with Domain Privacy Protection
- Contact your registrar or the party that helps you register the domain immediately without clicking on any links inside the email.
E – E-Payment Scam
Direct Damage: 😞😞😞😞😞
Future Damage: 😞
When your email account is compromised, scammers not only access your mailbox to read all your current emails, they will also create forwarder/filtering rules to monitor your email communication with your clients silently.
They wait patiently until the moment when you discuss payment details with your clients, and that’s the moment they jump into the email exchange (pretending they’re you) and offer your client fraud bank account details. A fraud case takes place when the client deposits the payment to the scammer’s bank account.

Suggestions:
- Do not access your email account using unsecured network/devices.
- Change your email login regularly with a strong password.
- Access control panel and double check if there are any unknown forwarder/filtering rules.
- Call your clients directly to clarify the payment.
Evil comes in different forms!
If you’re worried you might communicate with a Hacker or Scammer who does not fit into the above categories, please feel free to contact our team at support@domainplus.com.my













